I sometimes like to open my posts with a joke. But not this time. There isn't a joke for this.
Mrs. Dalai has cancer.
How's that for a kick in the ass?
I am neither vain nor arrogant enough to think that I could write the ultimate treatise on dealing with a loved one's cancer. There are any number of engaging stories out there on Caring Bridge and the like. You don't want to read a tear-jerker anyway, nor do you want to endure every last boring and/or gory detail. Mrs. Dalai would be very upset with me if I shared all that. Hell, she's probably going to be upset with me for writing this at all. She is a very private person, and does not like any of her personal details floating out there in cyberspace. Unlike me, of course. What I can deliver is a sort of gestalt, a seat-of-the-pants level series of vignettes, of observations, of feelings. Perhaps a few do's and don'ts for friends of those going through such things. In other words, I'm going to start typing and we'll see what comes out. As usual.
So...Where to start?
Mrs. Dalai had upper respiratory symptoms periodically throughout the Fall of last year. Naturally, we worried about COVID-19, but we weren't as petrified over the possibility as her then-internist, who wouldn't let her in the door without a negative COVID test. And another one. And ANOTHER one. And even then, he referred her to the ER rather than risk her coming in the office. As you might guess, he is no longer her internist.
We did finally get an imaging study, over a month after her symptoms began. I was standing in front of the modality monitor as it was acquired, and watched, paralyzed, as the wrenching turn in our lives was painted on the screen in all its grayscale horror. The tech, not grasping what he was seeing, pointed to the obvious and said, "Gee, what's that?" I didn't answer.
That was the beginning of an odyssey of visits to local clinics and hospitals, and a trip to one of the many Meccas out there. (A different Mecca insisted she come in person in the height of COVID-19 to be assessed, even though her pathology and imaging reports would tell the whole story. We didn't go there.) She went on to have chemo, radiation, several operations, two on an emergent basis, and was hospitalized for an entire month. Being on staff, I was allowed to stay with Mrs. Dalai 24/7, and I did. Aside from the two nights she spent in the Recovery Room, and two nights where I was able to hire a sitter, I was with her almost every moment. I do believe I deserve the Honorary Inpatient Award if there is such a thing. It would probably consist of my name etched onto a well-used bedpan. In red crayon.
Some observations from the wards:
Our hospitals had rolled out a very well-known EMR in the months before our sojourn. Not surprisingly, it was an unmitigated disaster. Order sets had been copied and pasted from elsewhere, and nobody knew nothin' about how the damn thing worked. Medications were at best delayed, and probably some were never given. Had I not been there, the wrong meds would have been administered on more than one occasion. Because EMR.
I don't know how other places do it, but here, the nurses all have their own full-sized computer on Mini-Cooper sized-carts. I guess no one in IT has heard of a laptop or a tablet. Because the EMR rules all, the nurses cannot do anything for their patients without the mammoth computer cart and so they push the monstrosities ahead of them when the enter the room. Thus, the room becomes quickly overcrowded, and the halls themselves are partially blocked by other Mini-Coopers hovering about, waiting their turn. At least they are easy to parallel-park. There has to be a better way to do this. Google Glass, maybe? Nah, too high-tech...
With a few notable exceptions, the nurses were spectacular. But they were stretched to the limit due to hiring freezes and staff reductions. Many told us they often went home in tears when their shift was over, and quite a few were planning on leaving. That is, those who were not already travellers. Funny how this staffing issue never strikes the C-Suite, nor do salary cuts.
Up to half of the nurses were not vaccinated. By their own choice. On the Oncology floor. I'll just leave that here for now.
We had a problem with one of the nurses' stations. It seems that around 3AM, many of the nurses and others dedicated to the welfare of their patients (or not) got bored, and they would have some very LOUD conversations. Since Mrs. Dalai's room was quite close to said station, we would be awakened by the din outside. AT 3AM. I finally had a chat with the Charge Nurse after a few nights of this. She offered to move us to a room down the hall, away from the racket. I responded in my best a$$hole doctor voice (yes, I have one, which I rarely use), "No, thank you, but you WILL be letting everyone know that making noise at 3AM is interfering with patient care and it is not going to happen again." It didn't.
Administration managed to get in the way of healing as well. My daughter, Dr. Dolly, just had our first grandchild, Dalai III, and we thought seeing him might cheer up Mrs. Dalai. So after receiving clearance from the oncologist (who examined the hospital's newly-revised visitation policy and found it supposedly welcoming) Dolly and her husband tossed their two-week old baby in the frunk of the Tesla (you don't really believe that, do you?) and drove the 12 hours down here to the Deep South. Once in the hospital, they were immediately turned in by do-gooder Nurse Karen on the Oncology Ward who suffered from the vapors and fainted on her divan, clutching her pearls on the way down, at the sight of a...a....BABY ON THE WARD!!!! In the days of COVID!!!!! Now you have to understand, Dr. Dolly got the vaccine while pregnant and actually wrote some of the national policy that guides such behavior. The kid was fine, and was not in any danger whatsoever. But the skittish, prissy nurse at the desk had alerted Administration to this horrific breach, and within 10 minutes, Nurse Ratched, Administrator of Pain, I mean Administrator of the Day, arrived at the door. "NO BABIES! IT'S AGAINST POLICY!!!!!" she said with the thin smile you see on people who love to wield power and torture small animals. We protested, explaining the obvious situation. But no. POLICY!!!! doncha know? Nurse Ratched even told my daughter that she should be "home healing" rather than visiting her mom. You can imagine how that went over with Dr. Dolly (who is an ObGYN herself). Funny how Nurse Ratched didn't direct her indignation at her colleagues who had yet to get the COVID-19 vaccine.
Someday I'll get around to informing the C-Suite of this fine inspiration of health and demonstration of compassion. It might have made a positive difference in Mrs. Dalai's outlook had she been able to hold III a little longer. But...POLICY. As I have found over the years with HIPAA, tortuous, self-serving IT security rules, and other similar things, COVID-19, or any other crisis, can on occasion be used rather nefariously to protect those who either want to avoid doing their job, or wish to dominate others around them. As you know from my previous missives, I cannot stand either mentality. Particularly when the health of my loved ones is impacted.
In the same vein (vain? vane?)...If you were managing a hospital, would you put the Oncology ward across the hall from the COVID ward? I wouldn't. 'Nuff said.
Anyway.
I got really sick of cafeteria food (some of which was occasionally available in the Doctor's Lounge...loved the Oreo chocolate pudding parfaits!) Subway had a sad little outpost within the hospital walls, and that helped, but there are only so many permutations of their ingredients, which I mostly exhausted after a week or so. I did use delivery now and then, but frankly, I wasn't all that hungry, and Mrs. Dalai's taste changed minute by minute. The nurses let me get my own bedding from the Clean Linen room, and I became very adept at making up the couch into a relatively comfortable bed. I became known as the one doctor in the hospital who would help them make the patient's bed. I got good at that, too.
There's more, of course, but I've probably already overstepped my bounds on certain issues. So sorry. I'm usually known for my restraint. Just ask certain PACS vendors.
Let me say a few words to those who are supporting a friend or relative with cancer, or really, any other serious malady, and supporting the patient's caregiver(s) as well. I should preface this by emphasizing that every situation is different. Each patient and each family member or caregiver has very individual wants and needs. What I say about me might not apply to someone else.
Most of our friends have asked repeatedly, "What can we do to help?" The honest answer is often that I don't know. I am more grateful for these offers than you could ever imagine, and I hope my friends don't take offense when I can't really respond. Cook something? Sure...wish I could have specified what would taste good when nothing struck Mrs. Dalai as the least bit appetizing. Come visit? She didn't want people seeing her at her worst. And so on. So I began to simply respond, truthfully, that what we really needed most was everyone's prayers. She has been the beneficiary of an amazing outpouring of good wishes and is on prayer-lists that literally span the globe. Yes, I do believe in the power of prayer. Very much so. If you also believe, please take a second and say a prayer for her. If you don't, do it anyway.
The concern was at times overwhelming, and this is where I might offer some advice. There were days while she was in the hospital that I spent an hour texting the daily "Mrs. Dalai Report" to the dozens of people asking about her. In fact, she sometimes looked over at me pecking away on Messenger and asked, "Are you on that damn phone AGAIN?" "Yes, dear, but for a good cause..." At first, I would try to individualize the text, but I later resigned myself to copying and pasting. On one particularly stressful day, I got lazy and sent a group text in a manner Apple assured me would not reveal the recipients to each other (it did anyway) and I accidentally pasted in the more detailed medical version rather than the streamlined USA Today-level prose. No big deal, but I learned my lesson. Back to copying and pasting.
Oh, yes, the advice...in essence, don't let your anxieties get the best of you. Which is a nice way of saying, don't call or text too often (like multiple times per day) and don't freak out if you don't hear something in some particular time-frame. If I was late with the daily report, several people would text (or call) fearing that something bad (worse?) had happened. But that only delays communications further. Rather like the ER phoning to ask why you haven't read Mrs. Jones' scan and in the process keeping you from reading it. I know they all meant well (except for the ER) and the concern is again much appreciated. But...
Believe it or not, there can be a negative side to caring. We have several acquaintances (I won't call them friends) who MUST KNOW every last gory detail of what's going on. And then they MUST SHARE these details with everyone else in their coven, I mean circle. I liken this to a bunch of kids trading baseball cards. ("I'll swap you Mr. McGillicuddy's splenectomy for Mrs. Smith's gallstones...") At the extreme, someone continuously texted me with a barrage of increasingly granular inquiries and then capped it off with the statement, "I have SO MANY questions!!!" I'm sorry, but that goes beyond caring and enters the realm of prying and even nagging. Please just allow me to give out the facts I think are needed, and let it go at that; in other words, have mercy on me and Mrs. Dalai. I did my best to keep these people happy and at arm's length, but it wasn't easy. We actually tried to hide the news from several such folk, attempting to keep Mrs. Dalai from becoming the topic of conversation around our little town, but of course that didn't work. I had occasion to discuss this with the hospital chaplain one day, and he analyzed it in this manner: "These people are very needy in their own way. They need your tragedy to feel better about themselves. Don't feed them, particularly while you and Mrs. Dalai are in genuine need yourselves." Spot on, Padre. Spot on.
And although I assume the best intentions, I don't need to hear about Cousin Schmuly, the best oncologist ever to grace the halls of some Mecca whom just everyone in the family consults for every funny looking freckle. We have a wonderful team of physicians here and we trust them 100%. And no, I'm not one of them. I do my best to avoid looking at her studies at all. I've still got PTSD from the slow-reveal of the initial image.
I can think of two questions that were asked, one innocently, one not so much, that should NEVER be uttered in these circumstance. The innocent question is one you might be surprised to learn has the unintended potential to deeply wound, and that is simply, "What is her prognosis?" That is a question one should NOT ask. EVER. Unlike the medical shows on television, there are no hard and fast answers. We can quote the odds, or the chances, or whatever, but remember, statistics do not apply to the individual. (Mrs. Dalai's oncologist actually went so far as to warn us against looking at those numbers.) Every day is another day, every day is precious, and we all take this journey through life one day at a time. We are not cartons of milk, only God can see the expiration dates stamped on our foreheads.
The other question, which was asked maybe innocently and maybe not by an acquaintance who in her late 70's is still quite concerned with body image was, "How much weight have you lost from Chemo?" Fortunately that question was posed in a phone call, and I wasn't on the line. Had I been, I would have jumped straight through the ether and throttled the other party. How vain and superficial can you get? Don't answer that...
In spite of all the love and support we have received, there is some degree of loneliness inherent in having a chronic illness. Mrs. Dalai often does not feel well enough to go out, but that's happening less and less. Still, she can feel a bit isolated. Hey, would any of you want to be locked up with me when you aren't feeling well? Or even if you ARE feeling well? Blessings to our friends who put up with our periodic cancellations of plans and such.
I think people often don't know how to be around someone with cancer, or other chronic illness. That one's easy. Just be yourself, let them be themselves. They are the same person they always were. They might be more fatigued, perhaps more irritable if they are experiencing pain. But they are still the person you know and love.
I wish I had something profound with which to end this little treatise. I really don't. How about "Cancer is bad!"? Does that work? Not really. How about the more optimistic "They are making great strides in treatment!"? That's a little better. And it's true. But the word "cancer" will always evoke feelings of dread in all of us. I'll never, ever, EVER get used to Mrs. Dalai's nonchalant tone when she says, "I have cancer," or something similar. It's a dagger through my heart. Every. Single. Time.
This is a long haul, for me and for her, but what was inevitably fatal when I was a medical student back in the days of stone knives and bearskins is no longer so. There are no guarantees, but for many, cancer can be cured, or at least kept at bay for a very long time. It seems that we don't use the word "cure" so much; rather, the favored term these days is Complete Remission, or CR. Please keep Mrs. Dalai in your prayers with that in mind.
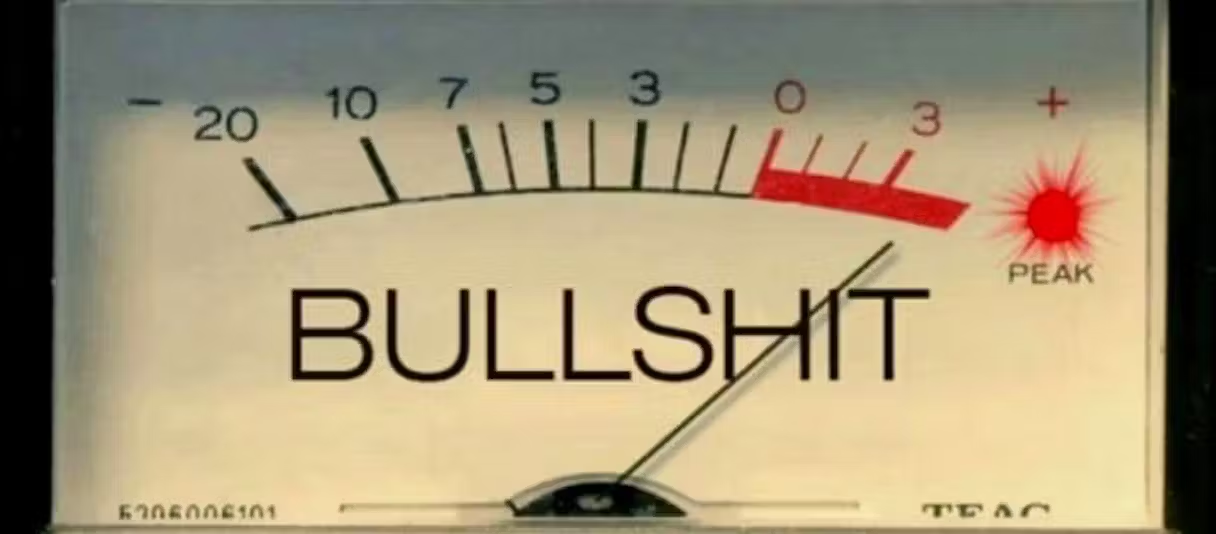
And if you smoke, stop. Right now. Today. NOW. Please. Oh, and take the damn COVID-19 vaccine TODAY if you haven't yet done so. Do it. Don't argue, don't quote any bullshit you've heard on Facebook or some other cesspool. JUST GET THE DAMN VACCINE NOW. We've had ours (and she's had the booster), with zero ill-effects. Please get it, not for yourself, but for the others you might save by not transmitting the virus. There are a lot of immune-compromised folks out there who will thank you. Starting with Mrs. Dalai.